Elyctis Identity Solutions
“Identity is who I am – Authentication is how I prove it” – Alexandre Joly, Elyctis CEO
Identity is quintessential not only to individuals but also to governments and other entities delivering services to citizens. More globally, modern states rely on government ID programs that ensure a unique identification of each citizen, guaranteeing their rights and duties. To complete these objectives, governments issue ID credentials to each citizen, with the appropriate security level.
ID credentials typically include Passports, ID cards, driving licenses, resident cards, etc. Nowadays, these ID credentials include security features that make reading them easy. Many ID credentials include a contact or contactless chip that contains biographical (name, date of birth, citizenship, …) and biometrical (fingerprint, photography, iris, …) allowing to identify the cardholder. Many ID documents also include a Machine Readable Zone (MRZ) that contains some information about the document holder as well as information needed to access the chip.


Once an identity document has been issued and delivered, services to be delivered to the citizens require an identity authentication. Several hardware and software solutions are available to complete this task, in a secure and privacy-sensitive manner.
European values drive how identity is to be handled to guarantee both the sovereignty of the State and the sovereignty of each citizen, who is entitled to decide how his/her identity will be used.
Reading ID documents requires a combination of different skills:
Optics: as documents are printed and especially contain printed elements such as the MRZ, readers implement a high expertise in optics, especially to read the MRZ in a single step, without additional movement for the user,
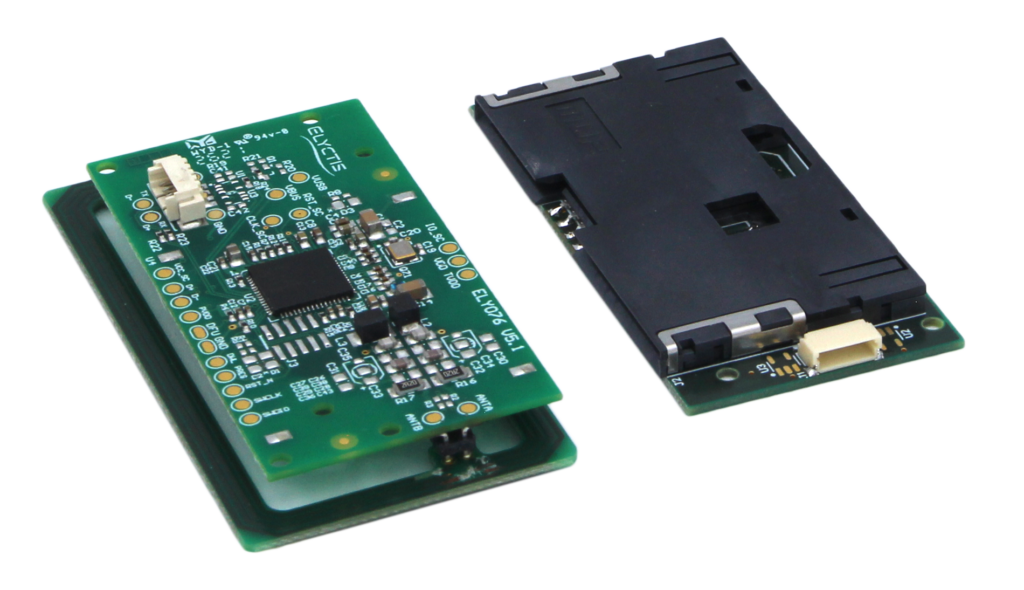
Electronics: as data is written in a contactless (or contact) chip, ID reading solutions have to implement contactless readers and use optimized routines to ensure the chip is read in a fast and accurate manner,
Software: ID reading solutions are built on software experience to ensure all data in the ID document are accurately and efficiently read,,
Security: as ID documents relate to individuals, an extra care is given to respecting privacy principles, and providing users needed data, but not more.
Over the years and thanks to its experienced staff, Elyctis has built the perfect combination of skills combining Optics, Electronics, Software and Security to serve the title of eID Expert.
Each of us has now a set of identities, defining citizenship, travel rights, enterprise security, ability to complete transactions, etc. Depending on the application context, each of these identities may require different tools to be verified. However, all of these identities belong to the same person, and authenticating that a person matches a given identity is capital.
Authenticating an identity document is actually a combination of several factors. To detect identity fraud, it is necessary to ensure that:
-
- The document is issued by an official authority,
- Data present in the document at the time of control have not been forged,
- The document has not been adulterated,
- Data has not been copied from a document to another one,
- Printed biographic information (name, date of birth, etc.) are the same as the information in the chip,
- The person presenting the document is its rightful owner, typically, this is verified thanks biometric technologies.
An efficient reading of an ID document goes through a combination of reading printed data, and photo, on the document and reading data from the chip. This is achieved thanks to an optical scanning of the document MRZ (Machine Readable Zone), combined with a reading of the document chip and a matching of biometric data.
Elyctis identity document readers come in all shapes and sizes: readers can be fixed or portable, they can be connected or standalone, they can be attached to a larger device or separate or be dematerialized and based on a smartphone app. Elyctis proposes a range of readers to cover all identification, verification, and authentication needs in the government identity environment.


Typically, the industry proposes two types of solutions:
-
- Fixed or mobile dedicated readers for Identity, which are the best adapted to specific requirements,
- Using a smartphone and an application to access the document, a solution which is more universal but often less user-friendly.
A dedicated reader may either have its own built-in security or be connected to a host that will execute security functions. Conversely, a smartphone can rely on either the built in smartphone security (thanks to a Secure Element, for instance) or establish a secure connection to the cloud.
Entities in need of authenticating identities will make decision depending on the application context:
-
- Most often sovereignty related applications such as border control, law enforcement or voting require dedicated readers as needs are specific and user friendliness is essential,
- Government document issuance also requires dedicated readers as they are used in an industrial environment,
- Final control at delivery of ID documents to the citizen could be considered both ways, but, in most cases, issuing authorities prefer to use a dedicated device,
- Depending on considerations including desktop space, connectivity, and versatility, the tourism and hospitality industry may go for either a dedicated reader or a smartphone based application,
- Banking and finance, industries in need of performing KYC (Know Your Customer) and AML (Anti-Money Laundering) checks and to verify the identity of transaction stakeholders, will pay an utmost attention to security, and may elect a dedicated or smartphone based solutions.
Verifying the identity of a citizens is always a sensitive action: both the citizen and the verifier must have a full confidence in the application. This means that either the reader is secure or security is brought by a secure application, relying on a Secure Element aboard the smartphone. A third emerging option is to establish a totally secure connection between a security server and the ID document itself going through a trusted independent device.
As citizens ID is a sensitive matter, it is the responsibility of the entity defining the application to choose the most appropriate and most secure solution. Security in identity verification often relies on the existence of a hardware Secure Element, which can be present in every reader, or in every handset, in connection with a remote secure server.
At Elyctis, we are proud of the expertise we have been building about government and non-government identity needs. Elyctis brings to the market its expertise in optical scanning and electronic reading of Identity Documents. We have a strong background in the secure transactions industry that leads us to know how to control electronic ID documents. Thanks to our longstanding experience in the identity field, we help our customers choose the most appropriate solution fitting their requirements.